SQL Server Developer Tips and Tricks
Latest SQL Server Tips
-
Comparing SQL Server and Oracle Backup Types

-
Reduce SQL Server Blocking with READ_COMMITTED_SNAPSHOT

-
Best Practices for Docker to run SQL Server on a Mac

-
PostgreSQL JSON and JSONB Data Types for Non-Structured or Semi-Structured Data

-
Migrate a SQL Server Database to a PostgreSQL Database

-
Getting Started with Azure CLI to Manage Azure Resources

-
Using Query Store to Identify CPU Intensive SQL Queries and Creating Proper Indexes

-
Add Indexes to Improve SQL DELETE Performance

SQL Server Tutorials
-
SQL Server SELECT Tutorial
-
SQL Server Stored Procedure Tutorial
-
SQL Server INSERT Tutorial
-
Visual Studio 2010 and SQL Server Tutorial
-
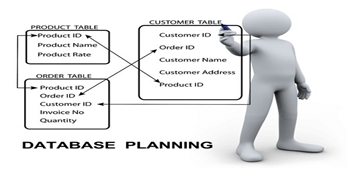
SQL Server Database Development Tutorial

-
SQL Server Data Tools (SSDT) SQL Project Tutorial

-
SQL Server Regex Tutorial

-
SQL Server Window Functions Tutorial


