By: K. Brian Kelley | Comments (22) | Related: > Security
Problem
I have a SQL Server login that's been locked out. I went to unlock it, but it's telling me I have to change the password to do so. I can't change the password and I don't know what it is. How can I unlock the account without changing the password? Check out this tip to learn more.
Solution
Starting in SQL Server 2005, SQL Server can use the password policies that the operating system uses. This includes account lockout. If a SQL Server login is configured to use password policy enforcement and your organization uses account lockout after a certain number of failed logins, you can end up locking out a SQL Server login via the same scenario.
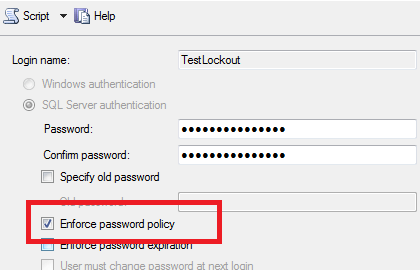
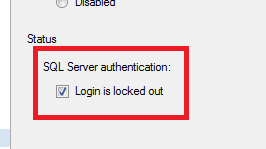
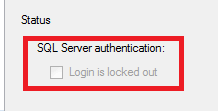
This can result in the account being locked out. Unlocking the account is easy to do if you want to reset the password. If you don't however, SQL Server won't let you directly. For instance, simply unchecking the box beside Login is locked out and clicking OK won't work.
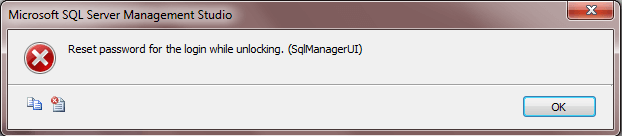
Instead, you'll get the following error:
The trick is to temporarily take the login out of password policy enforcement by unchecking it, as shown in Figure 4.
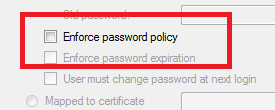
This will disable the unlock checkbox.
Click OK to confirm the change and the SQL Server login will unlock. This will permit connections via that login again. If there is a need for the password enforcement to be turned back on, you can do so and it won't re-lock the login. However, in either case be sure you know what caused the lockout in the first place. The reason for having account lockout is to prevent a security breach due to someone brute forcing the password for an account. Disabling password policy enforcement basically means an attacker can try to guess the password.
Next Steps
- Learn how to unlock the account using T-SQL with a password reset.
- Review how to check the password policy settings that will be applied by SQL Server.
- Understand the steps for disabling the sa login so it can't be attacked.
About the author
 K. Brian Kelley is a SQL Server author and columnist focusing primarily on SQL Server security.
K. Brian Kelley is a SQL Server author and columnist focusing primarily on SQL Server security.This author pledges the content of this article is based on professional experience and not AI generated.
View all my tips






